Have you ever wondered how your binary data is transferred across networks without any loss or
corruption?
Its due to the use of base 64 encodes and decode methods for data conversion and transfer. If you are
fond of data science or for that matter cyber security, you may have heard about base 64.
Honestly, there is little material published about this topic on the internet. Much to the dismay, the
published articles are so technical that they worsen the understanding of a reader let alone produce a
little clarity.
Defining base 64:
It is a type of encoding mechanism used in digital communication. Encoding, in essence, is the
conversion of data to a special format for different purposes like securing it from unauthorized people
to read to convert the data as the receiver wants to perceive.
Anyhow, base 64 encoding means converting binary data into text or ASCII strings across a network.
Here base 64 means that you have the liberty to represent binary data into 64 values.
Base 64 uses upper case and lower-case alphabets, 0 to 9 numbers, and signs like -, + or =. We often use
= at the end of the string. A typical base 64 string can use a maximum of two = signs at the end.
How any binary text is converted into ASCII string and encoded with base 64?
Suppose you want to send a message to another network across http, you first need to convert the text into binary and then your base 64 encoder converts it into corresponding ASCII string. Let’s see how it works.
ASCII is a standard used to represent binary data into the text in a computer system. As you know a computer understands binary language and processes data in the form of 0 or 1.
These are also called bits. To represent any text data such as language alphabets, computer scientists developed a standard encoding mechanism called ASCII.
It has almost 256 characters. Each character corresponds to a specific string of binary digits. You will understand it better through this ASCII conversion table.
For example, we convert the word “two” of ASCII in binary as:
t= 01110100, w= 01110111, o= 01101111.
Now ASCII format uses 256 characters which means it represents bits in the form of 8 binary numbers.
28 = 256.
As base 64 uses binary representation in 64 different values as 26 = 64. So, it represents binary in 6 bits.
Take the above example, the text “two” is represented in base 64 as:
t= 101101, w= 110000, o= 101000.
These binary digits are then encoded in base 64 as “dHdv”.
How to use base 64 encoding?
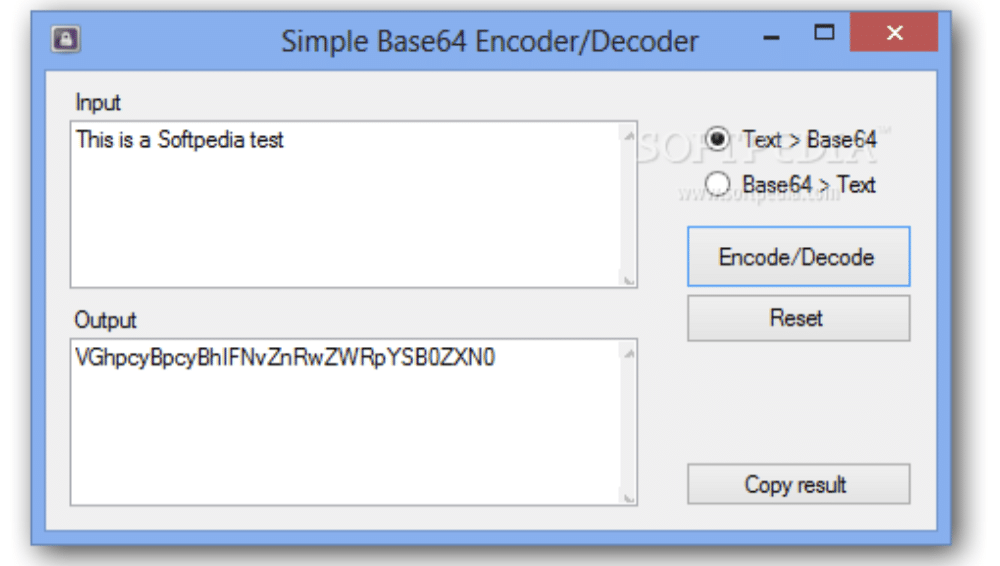
It was often very complicated to understand the relation of binary and base 64 as it is a pure data science subject.
There are several peculiarities and intricacies in dealing with this type of work. Therefore, you cannot manually do this type of tasks because each character has a corresponding digit or string in base 64 which seems gibberish when looked.
However, you can encode or decode base 64 strings easily with specific encoding and decoding tools. They take care of your conversion from one format to another easily.
Where is it used?
Base 64 is commonly used to transfer email data over the internet in a non-protected connection such as http. Therefore, we can say that it is used for data encryption because encodes any data.
Some data is used to transfer number while other binary data is used to stream text or images across the web.
To distinguish this issue, we use Base 64 because it encodes only those binary strings that are to be used as text in ASCII format. Hence, it is a very useful format to deal when it comes to data encoding.
Moreover, it can be an important encoding standard to understand the implementation of data science. Because it describes the relationship of different data representation formats.
Networks are prone to cyber hazards and data is often stolen easily if it is not protected. However, Base 64 encoding can help to cipher the data from stealth and to make it more secure.
On the flip side, malware creators can also capitalize from the use of this encode to disguise their malicious code into base 64 and outwit the reverse engineers.
Conclusion:
Base 64 encode is used in almost every communication across the internet particularly in emails. You can encode or decode texts through tools to better understand the transfer of data between networks.